The Language of the Network: Understanding Protocols
In any complex system, coordination requires a common language. In networking, these languages are called protocols. A protocol is a formal set of rules and conventions that regulate how devices on a network exchange data. Without these standards, a router from vendor A would be unable to communicate with a server from vendor B.
For telco engineers, understanding these protocols is the difference between “guessing” why a network is slow and “knowing” exactly which layer is failing.
The Architectural Foundation: The OSI Model
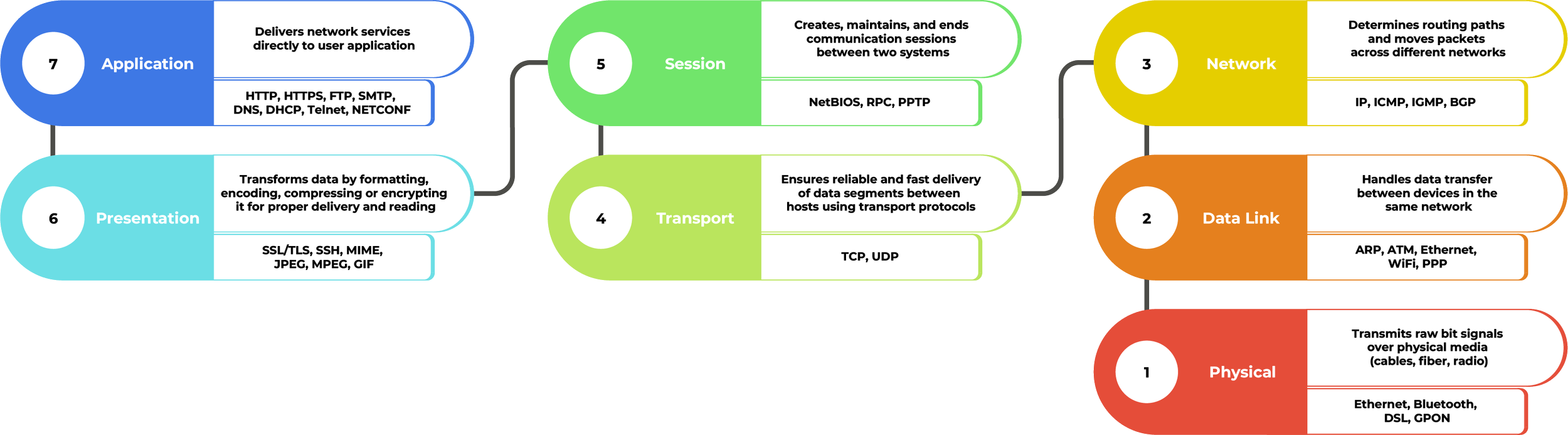
Before diving into specific protocols, you must understand the OSI Model. It is a seven-layer framework that describes how data moves from a physical wire up to the software application you are using.
Understanding this model allows you to isolate problems. If the “Physical Layer” is broken (e.g., a cut cable), troubleshooting the “Application Layer” is a waste of time.
Application Layer – Where Users and Software Interact
The Application layer is the topmost layer where applications interact with network services. It provides the interface for software to send and receive information.
HTTP (Hypertext Transfer Protocol): operates on a simple Request-Response cycle. When you click a link, your browser sends a GET request to a server, which responds with the HTML, CSS, and images needed to render the page. It is a stateless protocol, meaning the server doesn’t remember you from one request to the next without the help of cookies.
HTTPS (HTTP Secure): adds a vital layer of security by encrypting data using TLS (Transport Layer Security). This prevents “Man-in-the-Middle” attacks, ensuring the website you see is real and not a fraudulent interceptor.
FTP (File Transfer Protocol): is optimized for the reliable transfer of bulk data. It is unique because it often uses two different channels or ports: one for commands (list files, delete) and another one for the actual data transfer. This separation allows you to browse a server’s folder without interrupting a large download. While it was the gold standard for decades, it has largely been replaced by SFTP (SSH File Transfer Protocol) because standard FTP transmits your authentication credentials in plain text.
SMTP (Simple Mail Transfer Protocol), IMAP (Internet Message Access Protocol, POP3 (Post Office Protocol version 3): are the main protocols used for email communication. SM˜TP is responsible for sending emails, transferring outgoing messages from your mail client to mail servers, and between servers. IMAP and POP3 are used for receiving emails, but they work differently. IMAP keeps messages on the server and synchronizes them across multiple devices, making it ideal for accessing mail from different locations, while POP3 typically downloads messages to a single device and may remove them from the server.
DNS (Domain Name System): is often called the “backbone”of the internet, because without it, you would have to memorize the IP addresses of every site you visit. When you type a URL, your computer queries a DNS Resolver, which searches a hierarchical tree of servers to find the matching IP address. This process happens in milliseconds through a series of recursive lookups. Because this translation is so critical, DNS is a frequent target for hackers (DNS spoofing), which is why newer, encrypted versions like DoH (DNS over HTTPS) are becoming the new standard.
DHCP (Dynamic Host Configuration Protocol): is the network’s automated administrator that eliminates the need for manual IP addressing. When a device joins a network, it performs a four-step “handshake” known as DORA (Discover, Offer, Request, Acknowledge) to automatically obtain a unique IP address, subnet mask and gateway from a central server. By managing these addresses through temporary leases, DHCP can reclaim and recycle IPs from devices that disconnect, preventing IP conflicts and ensuring that all users can connect seamlessly without any manual configuration.
Telnet (Teletype Network): is a legacy protocol used for remote command-line access to network devices. It lets you type commands in a virtual terminal to manage a device remotely. However, Telnet is inherently insecure because it transmits everything, including authentication, in plain text. It has largely been replaced by SSH in modern environments.
NETCONF (Network Configuration Protocol): is a modern protocol gaining headwind in automating network devices. It uses structured XML data to send a receive configuration. It supports transactional operation, allowing you to commit multiple changes simultaneously or rollback to a previous state if an error occurs. For security, it typically operates over an encrypted SSH connection.
Presentation Layer – Making Data Understandable and Secure
The Presentation layer makes sure data is in the right format and, if needed, encrypted or compressed before it moves upward.
TLS/SSL (Transport Layer Security/ Secure Sockets Layer), SSH (Secure Shell): TLS/SSL is the gold standard for securing data in transit by providing encryption, authentication, and data integrity. While SSL is the older term everyone knows, modern systems actually use TLS to wrap application data in a secure tunnel that prevents eavesdropping and tampering.
Similarly, SSH provides a secure way to access and manage remote computers over an unsecured network. It replaces older, plaintext methods by using strong cryptography to protect login credentials and command-line instructions, making it an essential tool for system administrators.
MIME (Multipurpose Internet Mail Extensions): is the protocol that allows non-text files, such as pictures, PDFs, or audio, to be sent through systems originally designed for plain text. It works by labelling the data so the receiving application knows exactly what it’s looking at and which software to use to open it. Without MIME, your email attachments would arrive as a meaningless wall of code instead of a functional file.
JPEG, MPEG, GIF: JPEG is the standard for lossy compression of images, balancing file size and quality for web use, while GIF is used for simple graphics and short, looping animations. For video and audio, MPEG provides a suite of standards for high-quality compression, enabling the efficient streaming of massive amounts of visual data across the network without losing essential detail.
Session Layer – Keeping Conversations Open
The Session layer manages the dialogue between two systems. It establishes, maintains and terminates connections.
NetBIOS (Network Basic Input/Output System): is a legacy protocol suite that allows applications on separate computers in LAN (local area network) to communicate. Its primary role is to handle “Name Services”, allowing computers to identify each other by simple, human-readable names rather than complex IP addresses. It manages logical sessions between endpoints by establishing a connection, coordinating exchange of data, and then closing the session once the communication is complete.
RPC (Remote Procedure Call): is a mechanism that allows a program on one computer to execute a procedure on a remote computer as if it were running locally. It hides the network’s complexity from the application. The application simply calls a function and RPC handles the transport logistics of sending it to a remote server and waiting for the result. It is the underlying engine for many modern network services, acting as the bridge that lets distributed systems work together as a single unit.
PPTP (Point-to-Point Tunneling Protocol): is one of the oldest protocols used to build Virtual Private Networks (VPNs). It creates a tunnel between a remote client and a private corporate network, ensuring the connection remains active while data is transmitted. While it has largely been phased out in favour of more secure protocols like L2TP or OpenVPN due to its security vulnerabilities, it remains a classic example of how a protocol maintains a continuous, dedicated session over the public internet.
Transport Layer – Reliable vs Fast Delivery
The Transport layer is responsible for end-to-end communication, error correction, and flow control.
TCP (Transmission Control Protocol): is a connection-oriented protocol designed for high-reliability data transfer. It begins with a three-way handshake to synchronize sequence numbers and establish a virtual connection between the sender and receiver. Once data transmission starts, TCP uses acknowledgements (ACKs). The receiver must confirm the receipt of each segment. If an acknowledgement isn’t received within a specific timeframe, the sender assumes the data was lost and retransmits it. Additionally, TCP uses sequencing to reassemble packets that arrive out of order and flow control to prevent the sender from overwhelming the receiver’s processing capacity.
UDP (User Datagram Protocol): is a connectionless protocol with minimal overhead. Unlike TCP, it does not establish a formal connection, use sequence numbers, or guarantee delivery. It simply packages data into datagrams and sends them to the destination immediately. UDP includes an optional checksum for basic error detection, but has no built-in retransmission or ordering mechanisms, making it significantly faster than TCP. This makes it the standard protocol for time-sensitive traffic where the occasional lost packet is preferable to the delays caused by retransmission, such as in DNS queries, DHCP, and real-time media streams.
Network Layer – Finding the Path
The Network layer handles the routing of data packets from the source to the destination across different networks.
IP (Internet Protocol IPv4, IPv6): serves as the fundamental mechanism for addressing and routing packets. IPv4, the long-standing standard, utilizes a 32-bit addressing scheme, which limits the total number of unique addresses to approximately 4.3 billion, a number that has been exhausted by the explosion of internet-connected devices.
IPv6 was developed to provide an vast address space, using 128-bit addresses. Beyond quantity, IPv6 improves efficiency with a simplified, fixed-length header that reduces the processing load on routers, and eliminates the need for Network Address Translation (NAT) by providing unique global addresses for every device.
ICMP (Internet Control Message Protocol): is used by network devices to send error messages and operational information. It does not carry user data but is vital for diagnostics. For example, when a destination is unreachable, ICMP generates a notification for the sender. It is the underlying protocol for tools like ping and traceroute.
IGMP (Internet Group Management Protocol): is used by hosts and adjacent routers to establish multicast group memberships. It allows a network to efficiently direct a single data stream to multiple specific subscribers simultaneously, rather than broadcasting it to every device on the network or sending individual copies to each user.
BGP (Border Gateway Protocol): is the routing protocol that makes the internet function on a global scale. It is used to exchange routing and reachability information between different Autonomous Systems (large networks or ISPs). It determines the most efficient path for data to travel across the vast web of interconnected global networks.
Data Link Layer – Local Network Delivery
The Data Link layer handles the physical movement of data between two devices on the same network segment.
ARP (Address Resolution Protocol): is the critical bridge between the Network Layer and the Data Link layer. While IP addresses (layer 3) are used for routing across networks, hardware devices communicate locally using MAC addresses. When a device knows the IP address of a destination on the same network but lacks its physical hardware address, it broadcasts an ARP request. The device with that IP responds with its MAC address, allowing the sender to map the two addresses together and successfully encapsulate the data into a frame for delivery.
ATM (Asynchronous Transfer Mode): is a high-speed networking technology that carries voice, video, and data simultaneously over a single network. Unlike Ethernet or Wi-Fi, which use variable-length packets, ATM uses small, fixed-size cells of exactly 53 bytes. This uniformity allows hardware to process data at extremely high speeds with predictable timing. While it has largely been superseded by IP-based technologies in local networks, it remains a foundational part of many wide-area network (WAN) architectures.
Ethernet (IEEE 802.3): is the most widely used protocol for wired Local Area Networks (LANs). Defined by the IEEE 802.3 standards, it dictates how data is formatted and transmitted over physical cables to ensure compatibility between different hardware manufacturers. Ethernet uses a contention-based media access method, where devices check for existing traffic before transmitting. It organizes data into frames, which include error-checking codes (Cyclic Redundancy Check) to ensure the data arrives at the destination without being corrupted during transit.
Wi-Fi (IEEE 802.11): is the wireless counterpart to Ethernet and operates under the IEEE 802.11 family of standards. Unlike wired connections, Wi-Fi must deal with the complexities of shared airwaves, interference, and physical obstacles. It uses a specific mechanism called CSMA/CA (Carrier Sense Multiple Access with Collision Avoidance) to coordinate transmissions. Instead of just detecting collisions like a wired network, Wi-Fi devices attempt to avoid them by transmitting a brief signal to clear the air before sending the actual data frames.
PPP (Point-to-Point Protocol): is a protocol used to establish a direct connection between two nodes, commonly used in long-distance telecommunications or for connecting a home computer to an Internet Service Provider (ISP). It provides features that simple Ethernet does not, such as authentication, encryption, and data compression. It is highly versatile, as it can simultaneously carry multiple network-layer protocols (like IPv4 and IPv6) over the same physical link.
Physical Layer – The Actual Signal
The Physical Layer deals with the mechanical and electrical specifications of the transmission medium (cables, radio waves, etc.).
Ethernet: defines the specific cable types and the electrical signaling levels used to transmit data over copper and fiber. It also defines the shape of the plug and how fast the electricity blinks to represent data.
Bluetooth: is a radio wave used for short-range communication. It’s all about frequency hopping, quickly jumping between radio channels to avoid interference from your microwave or Wi-Fi.
DSL (Digital Subscriber Line): is using old copper telephone lines to carry digital data. It uses different frequencies, so you can use the internet and talk on the phone at the same time.
GPON (Gigabit Passive Optical Network): is the modern fiber-optic internet. It uses light impulses sent through glass strands and uses splitters to share one main fiber line with an entire neighbourhood.